RULES OF THE ROAD
TOPICS BELOW
Most Important, Other Rules,
Scam School, Companies to Avoid,
And Again
MOST IMPORTANT
This website is huge, so if you read nothing else here, always remember these most basic rules of the road.
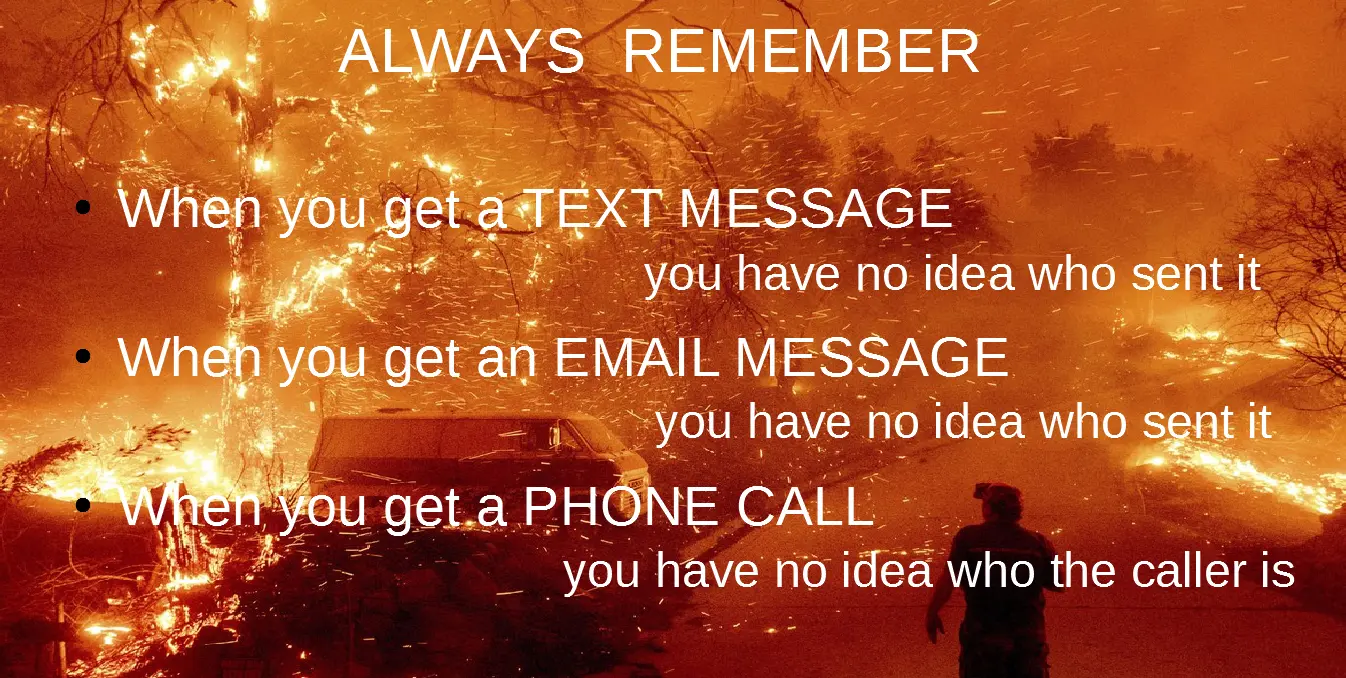
- When you get a text message, you have no idea who sent it
This article tells of a Fidelity customer that got a scam text message claiming to be from Fidelity. Then they got a phone call from the bad guys, again claiming to be Fidelity (more on this below). Then the bad guys tricked Fidelity into sending the victim a temporary code by impersonating the victim at the Fidelity website. The victim reads the temp code back to the bad guys on the phone, and good-bye $$$.
What Does a Thief Need to Access Your Financial Accounts? It’s Likely Less Than You Think by Mike Piper February 9, 2026. - When you get an email message, you have no idea who sent it.
The FROM address of an email message can be forged. Or, the FROM address might use a look-alike domain name. Even if the FROM address is correct, the email account that sent the message may have been hacked. And, there have been assorted hacks where the systems of legitimate companies have been tricked into sending emails. If a message seems legit because it discusses things about you, this knowledge may well have come from a data breach. Data breaches are, sadly, a very common thing.
More here: 'From' Spoofing: How Spammers Send Email That Looks Like It Came From You by Leo A. Notenboom. Last updated Nov. 24, 2025 - When you get a phone call, you have no idea who the caller is.
The CallerID can be forged. If the voice sounds familiar, voices can be cloned and the technology has been proven to fool a mother into thinking her daughter was calling. And, as will email, if it seems legit because the sender knows things about you, this knowledge may well have come from a data breach. - Any photo/picture can be faked, no matter how real it looks
- Any video can be faked, no matter how real it looks
- Any audio can be faked
ACT ACCORDINGLY. In other words: Always be skeptical. Always. Always. Always.
In March 2022, Russia invaded Ukraine, which prompted this article: Here’s how to avoid Ukraine charity scams in the Washington Post. Quoting: "To avoid a scam using the conflict in Ukraine ... start with the premise that every direct message, link, email or text is fake and work from there. This should be your default response to any contact you did not initiate".
OTHER RULES top
Don't advertise to the world (Facebook, Instagram,etc) when your home will be empty (such as going on vacation).
If you are prompted to install software, don't do it. This advice comes from Brian Krebs. Non techies can be easily scammed into installing malicious software because they don't know what software is really needed to perform any given task. In October 2023, Krebs wrote that "One of the oldest malware tricks in the book - hacked websites claiming visitors need to update their Web browser before they can view any content - has roared back to life in the past few months." The article is about a new wrinkle in the scam, hosting malware on a blockchain, but this is not important for Defensive Computing. The important point is that without detailed technical knowledge of the software, the safest thing to do is to say no.
Non-technical computer users should use a Chromebook. Compared to all other mainstream operating systems, ChromeOS (the name of the operating system on a Chromebook) is much more secure and requires no care and feeding. Also, no viruses. Only computer nerds should use Windows.
Do not re-use passwords. I know this is hard as it requires a system for managing the dozens of passwords we all need to keep track of. At the least, use different passwords for the most important accounts. Which accounts are the most important is up to you but certainly financial and email. I wrote a long article on passwords, The worlds best password advice where I introduce the concept of a password formula. It can provide reasonably secure, reasonably unique passwords that are easy to remember and safe to write down on paper.
The price of free software and free services is no technical support. And, probably being spied on.
- Email is worth paying for. The most obvious reason is for tech support if something goes wrong. Also, to avoid being spied upon by the provider of a free email service. Then too, to insure the account remains available even if it goes unused for a long period of time. As a rule, we depend on email for many things and the loss of an email account can be a very big deal.
- If you use a free email service, do not let it sit, unused, for too long. Also periodically check the phone number and email address that is on file for recovery purposes is still valid. More.
- The more email addresses you have the better. There is, however, no simple way to achieve this. The available options are on this site, here: Multiple Email Addresses.
SECURE EMAIL
- Email is not private. You may see talk about email encryption, but that only applies to messages as they travel over the Internet. Once they come to rest in your inbox or the inbox of your recipient, they are not private.
- Two exceptions are Proton Mail and Tuta (formerly Tutanota). Messages from one Proton Mail user to another Proton Mail user are fully private. The same for Tuta. However messages from either one to anywhere outside of their little worlds are not private. Both companies offer free, limited, accounts that you can sign up for anonymously.
- Both Tuta and Proton Mail are simple webmail, something everyone can use. No software to install or learn. Thus, they are a great solution for Secure Messaging. The world recommends Signal and the world is wrong. Both Proton and Tuta can be used on a Chromebook in Guest mode to insure that they leave no traces behind which makes them more secure than Signal. And, there is no need to install a mobile app. Any app that runs on Android or iOS will never be as secure as a Chromebook, especially in Guest mode. Signal messages are only secure when sent to other Signal users, same as Tuta, same as Proton Mail. Signal requires a phone number, so not at all anonymous. With webmail, the public and the companies can see the FROM and TO email addresses but they can not see the body of the messages. Proton can also not see into any attached files. Not sure about Tutanota and attachments.
WEBSITES
- When you have a choice, using the website of a company/service is safer than using their mobile app (think Facebook, TikTok, etc). By safer, I mean more private, a web browser spies on you less than an app. Web browsers offer more control over what a website can learn about you. You can control whether it is allowed to know your location. You can install assorted blocking extensions in a web browser. You can use private browsing mode to limit the data the website leaves behind. You can see the ads/trackers it uses in a number of ways (varies by OS and browser). Want proof? The website will nag you to install the app but the app will never nag you to use the website. What is better for them, is worse for you.
- Phones get lost and stolen. Should this happen to you, it would be better if the app for your financial institution(s) were NOT on the phone. Use their website instead. Or, install their app on a tablet that stays at home.
- July 30, 2025: From Jeannie Warner on Mastodon: "A friend who works at Meta recommended that one only interact with Facebook in a web browser. Don't download the app."
- June 3, 2025: Meta and Yandex are de-anonymizing Android users' web browsing identifiers by Dan Goodin for Ars Technica. Apps from Facebook, Instagram, and various Yandex apps are spying on the web browsing of Android users in a somewhat new way. Javascript code embedded in many websites communicates with these apps, even though the apps are not running in the foreground. If the apps were not installed, this spying would not have been possible.
- October 23, 2024: The Global Surveillance Free-for-All in Mobile Ad Data by Brian Krebs. In this case, someone was put in serious danger by the spying done by the Macy's app on their phone.
WEB BROWSERS
- Have 2 or 3 installed and available web browsers. Sometimes, things will work in one and not another. If one gets corrupted with malware, you will have a fallback.
- The security around browser extensions is disgraceful. As a starting point, install just uBlock Origin and nothing else. As of March 2025, Chrome no longer allows uBlock Origin, so use uBlock Origin Lite instead. Some sites you care about depend on ads, so may want to configure uBlock Origin to allow ads on just those sites.
- On Windows, macOS and Linux, install Firefox or LibreWolf. On Windows, install the portable version of Firefox at portableapps.com and/or the portable version of LibreWolf.
- If you really need a particular browser extension, install it into only one web browser and limit the use of that browser.
- Use Private Browsing Mode as often as possible.
Another way to block ads and trackers is with DNS, the system that translates computer and website names into their underlying numbers (IP addresses). Some services translate anything and everything, while other services will not translate known trackers or ads or porn. Different DNS services offer different options. I am a big fan of NextDNS, but setting it up may be too much for someone without a technical background. It is worth the effort, however. NextDNS can be configured on either the operating system level or just for one web browser. A good starting point is the DNS Tester Page on my Router Security website.
You are safer, when away from home, if the Wi-Fi is turned off on your phone. This is a great example of how increased security always requires an increased hassle. The problem with this rule, is that if you fail to turn the Wi-Fi on when at home, your phone will use 4G/5G/LTE and the increased data usage may cost you money.
Hidden information inside a photograph can give away the location of where the picture was taken. The hidden/non-visible information is called either metadata or EXIF data. There are two approaches for not revealing metadata. One is to turn off location data when sharing a picture. The other option is turn off location tagging in the camera app on your phone. To see all the hidden data attached to an image, upload it to the Online EXIF viewer. You may see nothing (no metadata found), you may see a location given in both longitude and lattitude or you may see technical details of the photo and the camera that took the photo.
Advice from the mainstream media, such as the New York Times, the Washington Post and the Wall Street Journal is frequently bad. For whatever reason, they hire reporters, not nerds. You should not take technical computer advice from anyone without a technical computer background. No one writing for the mainstream media has a technical computer background. They may mean well, but they are rarely qualified to offer an opinion.
Avoid the cheapest Android devices. That includes phones, streaming TV devices and tablets. Especially avoid devices without a name brand. These things have often come with malicious software pre-installed. Another potential problem is the battery. I purchased an onn Android tablet from Walmart. Big mistake. The battery swelled up which is quite dangerous. I suspect that hardware or software that prevents this sort of thing costs money and a low end tablet will cut every corner it can.
When installing Android apps, be very careful that you have the real app, not a scam copy. Google does a very poor job in this regard, so it falls on you. You need to verify not only the name of the app, but the developer too. And the name must be an exact match for what you are looking for.
If you mother tweets something, don't believe it. Twitter is full of lies and liars.
Your Internet Service Provider (ISP) can see much of what you do. Not everything, but enough to learn quite a lot about you. Thanks to HTTPS secure websites they can not see the contents of every web page you view, but they can identify every website you visit and when you visit it. The solution to this is to use a VPN (Virtual Private Network).
If you depend on a VPN for privacy, do not use iOS devices. Apple sends data to their own servers outside of the established VPN tunnel. This has been ongoing for a long time and Apple can not be shamed into doing the right thing.
Avoid crypto currencies (aka crypto) and NFTs.
VPNs are a good thing, but finding a trustworthy one is the difficult part. The VPN page here addresses this and its h-u-g-e. The first rule of VPNs, however, is to avoid the free ones.
Good news: You can safely ignore Passkeys, they are nothing more than a password that you are not allowed to know. It is a fad and like all fads, will fade away.
What goes up, must come down. OK, that was a joke.
Many credit cards can send you an email for every charge when the credit card was not physically present. In my experience, this has been a free service. It is a great way to immediately learn if a bad guy is charging stuff to your credit card.
To prevent a bad guy, armed with all your personal information from opening a new credit card in your name, freeze your credit reports.
Anyone with Apple devices, should read this: What to expect when in contact with Apple Support from Apple September 16, 2024.
If you receive an unprompted two factor code (typically via a text message) it probably means that bad guys have the password to whatever site/system sent the 2FA code. You should log into that site/system and change the password ASAP. From: What to do when receiving unprompted MFA OTP codes by Lawrence Abrams for Bleeping Computer. December 17, 2023.
Employees: Maintain a work cellphone and a personal cellphone. Do not use employer-supplied devices for anything personal. Do not let your employer or their IT department install anything on your personal devices. Here is a worst-case scenario of what can happen from Chris Patti (September 2025).
Don't buy cheap Lithium Ion batteries. From: X-ray scans reveal the hidden risks of cheap batteriesby Andrew Liszewski for The Verge. September 24, 2025
Avoid very cheap USB flash drives. The storage capacity that they claim to have can be faked. The faking extends to your operating system which reports the scam capacity. In fact, your operating system is likely to show nothing wrong because the flash drives lie to the operating system about the success of writing data, always reporting that it worked. Even formatting the thing reports no errors. This situation prompted Steve Gibson to create his ValiDrive program (only works on Windows) in September 2023.
SEARCH ENGINES
- Don't do Google searches while logged in to Google. This is a relatively easy one :-)
- Whatever search engine you use, be very attuned to which search results are ads and which are not. The indication that something is an ad, can be very small and easy to miss. Some ads are scams that try install malicious software.
- Do not trust Google, or any search engine, for customer service phone numbers. Bad guys fool search engines to scam people. Go to the website of the company you want to call.
SCAM SCHOOL top
April 26, 2026: This topic has been moved to its own page. See Scam School.
COMPANIES TO AVOID top
Some headaches/hassles can be avoided by not dealing with companies that have done assorted bad things. The list of companies to avoid has been moved to its own page.
And, again top
Act accordingly.